Chain Of Custody Form Template - We use a security bag chain of custody system. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. Page ___ of ___page ___ of ___ When we receive evidence into our lab (or collect it in the field), all items are. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. 1) it depends on the situation.
Page ___ of ___page ___ of ___ When we receive evidence into our lab (or collect it in the field), all items are. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. We use a security bag chain of custody system. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. 1) it depends on the situation.
Page ___ of ___page ___ of ___ The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. 1) it depends on the situation. We use a security bag chain of custody system. When we receive evidence into our lab (or collect it in the field), all items are. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed.
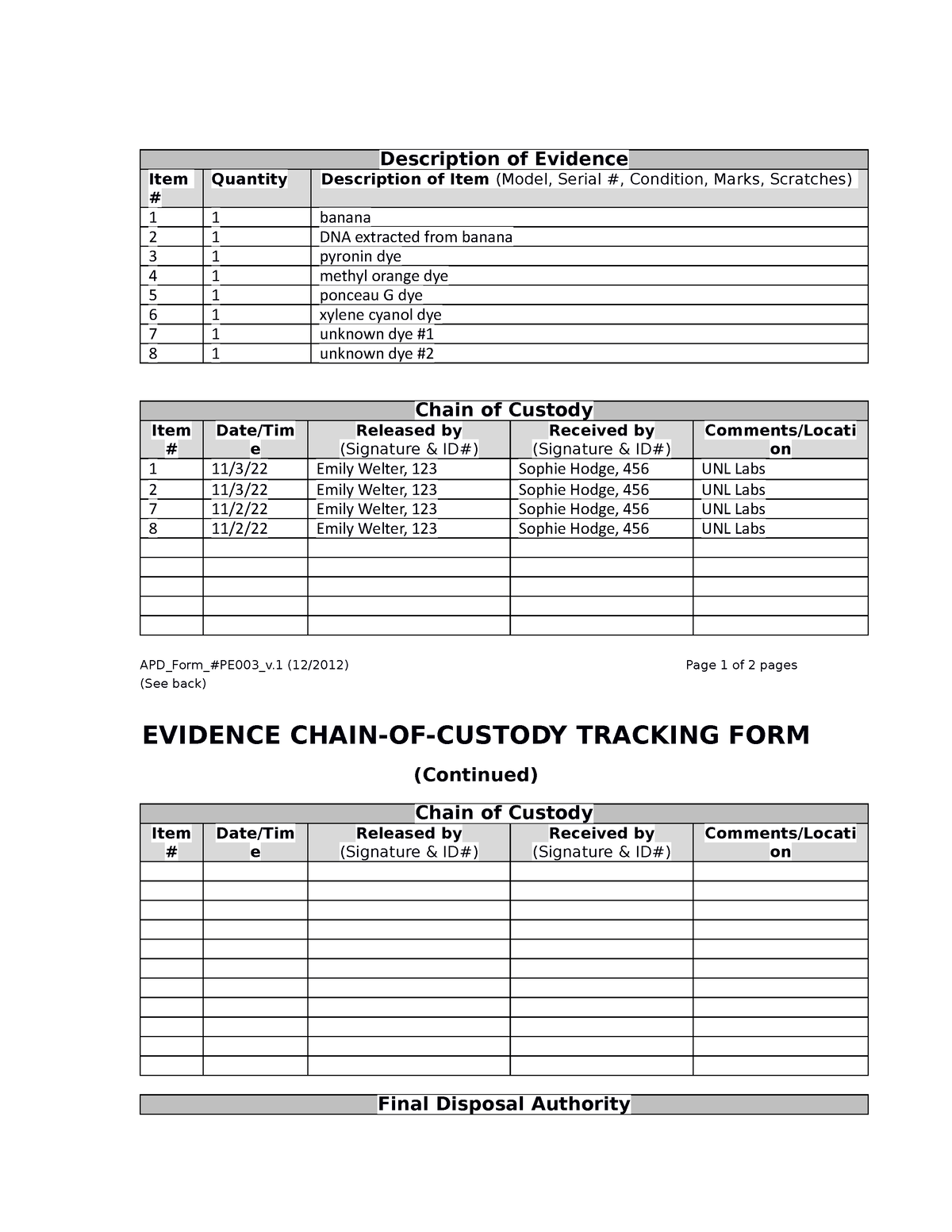
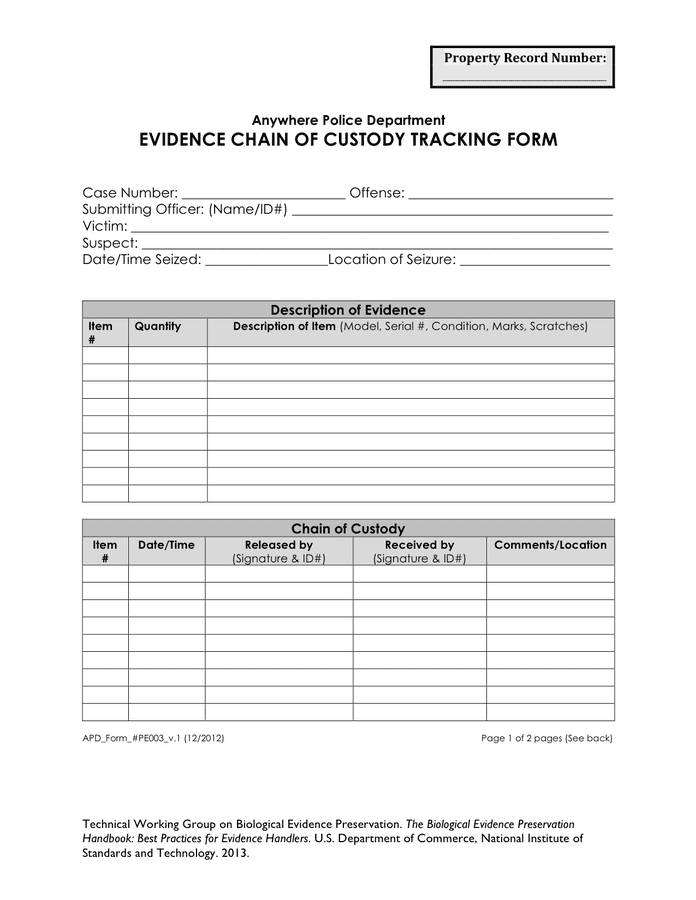
Sample chain of custody form in Word and Pdf formats page 2 of 3
I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. We use a security bag chain of custody system. When we receive evidence into our lab (or collect it in the field), all items are. Page ___ of ___page ___ of ___ 1) it depends on the situation.
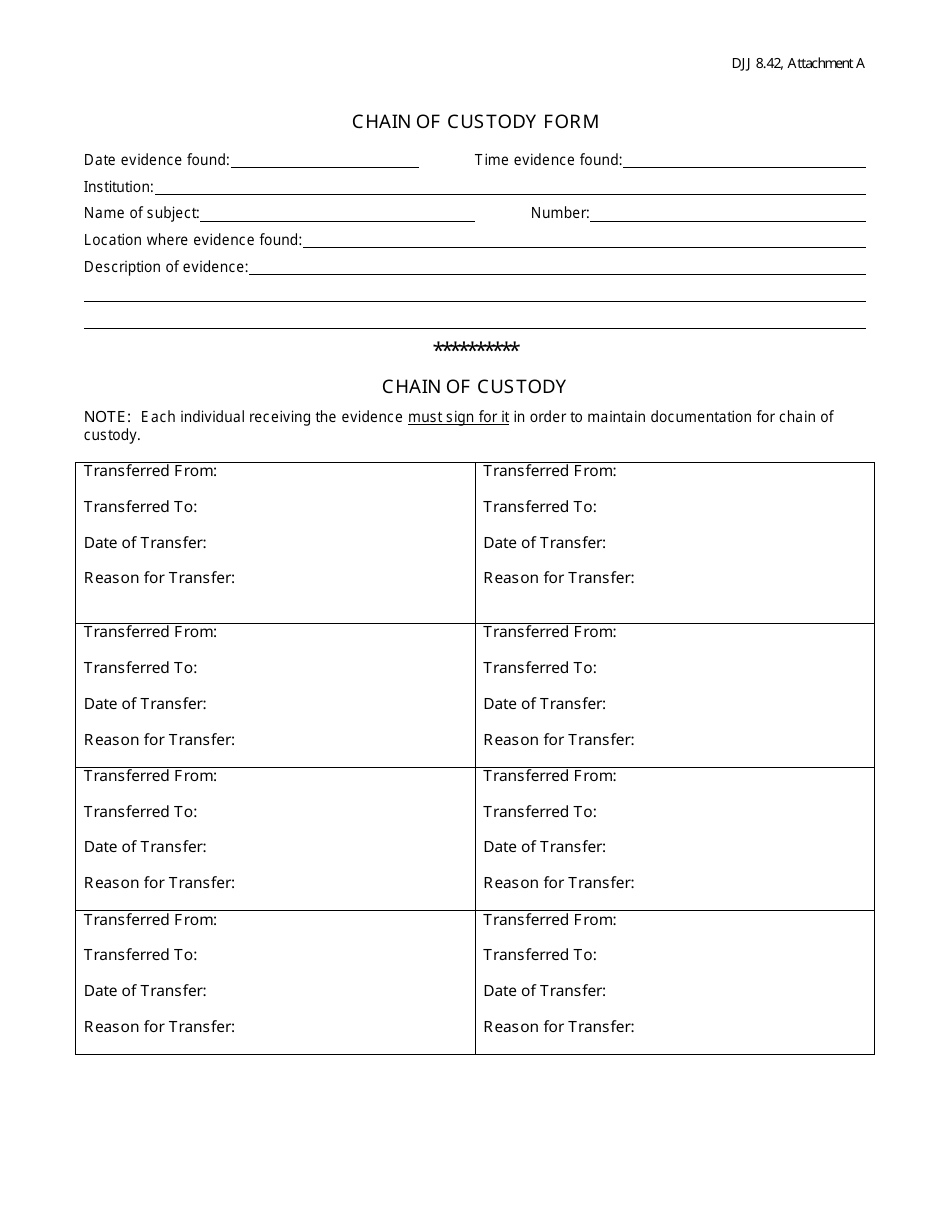
Printable Chain Of Custody Form Template
When we receive evidence into our lab (or collect it in the field), all items are. Page ___ of ___page ___ of ___ We use a security bag chain of custody system. 1) it depends on the situation. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed.
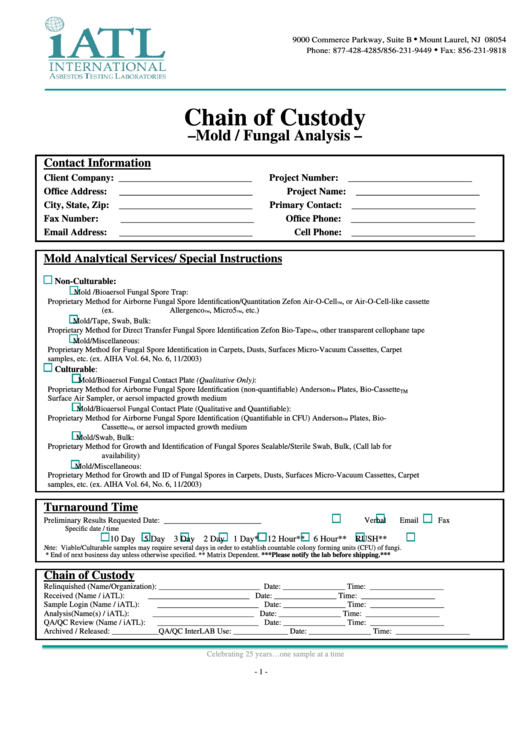
Fillable Online Chain of Custody Documentation Form Fax Email Print
When we receive evidence into our lab (or collect it in the field), all items are. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. 1) it depends on the situation. We use a security bag chain of custody system. Page ___ of ___page ___.
SampleChainofCustodyForm lab 9 Description of Evidence Item
Page ___ of ___page ___ of ___ We use a security bag chain of custody system. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. When.
Printable Chain Of Custody Form Template
When we receive evidence into our lab (or collect it in the field), all items are. 1) it depends on the situation. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. Page ___ of ___page ___ of ___ We use a security bag chain of.
Printable Chain Of Custody Form Template Free Printable
The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. We use a security bag chain of custody system. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. 1) it depends on the situation. When we.
Printable Chain Of Custody Form Template Printable Templates
I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. Page ___ of ___page ___ of ___ 1) it depends on the situation. When we receive evidence into our lab (or collect it in the field), all items are. The paper did not solve the problem of the digital evidence chain.
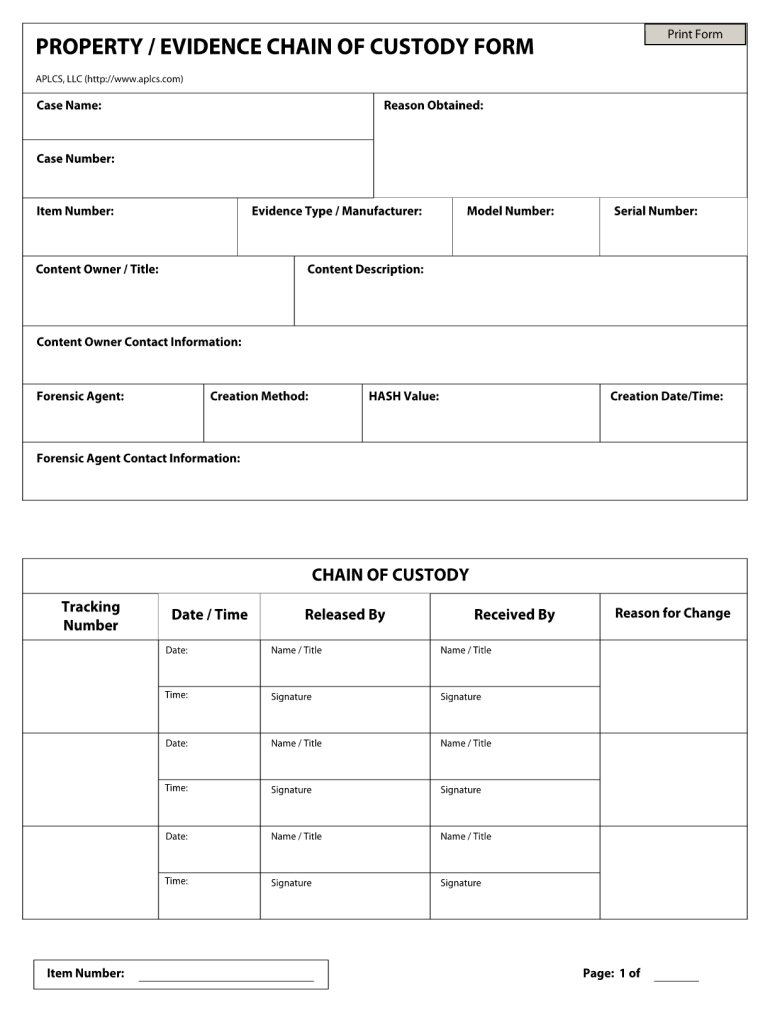
Chain of Custody Form Digital Forensics Data Management
1) it depends on the situation. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. We use a security bag chain of custody system. Page ___.
Chain Of Custody Form Example Fill Online, Printable, Fillable, Blank
The paper did not solve the problem of the digital evidence chain of custody, and the ontology was used only to define the vocabulary. When we receive evidence into our lab (or collect it in the field), all items are. Page ___ of ___page ___ of ___ We use a security bag chain of custody system. 1) it depends on.
Sample chain of custody form in Word and Pdf formats
1) it depends on the situation. Page ___ of ___page ___ of ___ I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. When we receive evidence into our lab (or collect it in the field), all items are. We use a security bag chain of custody system.
The Paper Did Not Solve The Problem Of The Digital Evidence Chain Of Custody, And The Ontology Was Used Only To Define The Vocabulary.
Page ___ of ___page ___ of ___ 1) it depends on the situation. I figure the image, evidence found on the image, hash values, and chain of custody logs are all needed. We use a security bag chain of custody system.